Galaxy S5 Receives Official Android 5.1.1 Update with Stagefright Fix – How toAndroid Stagefright security update is now available for Samsung Galaxy S5. This is an important update coming to fix the Stagefright Android vulnerability. With Stagefright vulnerability, all the attackers need is your mobile number to remotely execute malicious code using a specially crafted message. This is an extremely serious vulnerability as the target doesn’t need to do anything unlike in the spear-phishing attacks where victim falls to some trap. Google has now fixed the bug which means you should update your devices as soon as you receive the notification of this patch.
Samsung and T-Mobile are releasing this official update to users in multiple stages; users will start receiving the OTA notification in the coming days. However, if you want to flash this security update right away, here is how to manually do so.
Note: This is an official Android 5.1.1 security update for T-Mobile Samsung Galaxy S5 model SM-G900T. Please do not try it on other variants. Flashing updates manually could void your device’s warranty; only proceed if you know the risks associated with the process.
Prerequisites to update Galaxy S5 to G900TUVU1FOG6 Android 5.1.1:
- Create a backup of all important data in your Galaxy device.
- Download and install USB drivers for Samsung Galaxy S5 in your computer.
- Enable USB debugging option by pressing Menu > Settings > Applications. Navigate and tap on Developer Options to ensure that USB Debugging is enabled.
- Ensure that your T-Mobile Samsung Galaxy S5 G900T carries more than 80% of charge.
How to flash G900TUVU1FOG6 Android 5.1.1 on Galaxy S5 to fix Stagefright:
Files required: download G900TUVU1FOG6 Android 5.1.1 for T-Mobile Galaxy S5. Also download Odin3 v3.10.6 for installation from here. Unzip Odin; and unzip the official firmware file to get the .tar.md5 file.
- Install Odin on your PC and launch it.
- Switch your Samsung Galaxy S5 off and boot it in Download mode: press and hold Volume Down, Powerand Home buttons together.
- Connect your SGS5 via a USB cable; when connected successfully, you will get a message in Odin saying Added!!. (In case you don’t get it, try another USB port. If that doesn’t help either, then re-install USB drivers).
- Click on AP in Odin and locate the G900TUVU1FOG6 .tar.md5 file.
- In Odin make sure to uncheck Re-Partition. Hit START.
- When update installation is successfully completed, you will see your T-Mobile Samsung Galaxy S5 rebooting.
First boot takes a few long minutes so please be patient.
User Tag List
 Likes: 0
Likes: 0
Resultados 61 a 72 de 72
Tópico: Android 5.1
-
19-08-15, 07:55 #61Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
-
19-08-15, 16:01 #62Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Trend Micro Finds MediaServer Vulnerability In Android, Affecting Most Devices
Noticia: Security researchers from Trend Micro uncovered yet another media-related vulnerability, this time in the MediaServer program. Attackers can exploit this vulnerability to run arbitrary code on the devices, giving it the same permissions as the MediaServer program itself.
Security researchers from Trend Micro uncovered yet another media-related vulnerability, this time in the MediaServer program. Attackers can exploit this vulnerability to run arbitrary code on the devices, giving it the same permissions as the MediaServer program itself.
The vulnerability affects all Android versions from Android 2.3 to Android 5.1.1, but Trend Micro stated that Google has already pushed a fix to the Android Open Source Project on August 1. Trend Micro made Google aware of the bug on June 19.
The security company also said that it hasn't seen any exploits of this vulnerability in the wild so far. However, knowing the big problem the Android ecosystem has with updates, only a small part of the existing devices will fix this vulnerability in the future, while most of the others will remain vulnerable to it.
The attackers can use the vulnerability to ask Android users to install an app, which doesn't require any permission, making the user think it's safe. The attack can be fully controlled by the malicious hacker, who can start or stop it at any time.
The attacker's code gets the same permissions as the MediaServer program, which has the ability to perform many media-related tasks. This includes taking pictures, reading video files, recording video, all of which can put the user's privacy at risk.
According to the Trend Micro researchers, the attack can be quite stealthy, making it hard to detect and the attacker may not even trigger the attack for months after the device is infected.
The best course of action against this bug would be to upgrade your device once the patch is ready from your phone's manufacturer. If no such patch is received or you don't want to wait until then, Trend Micro's Mobile Security app will also detect malicious apps that want to take advantage of this vulnerability.
The company also said users could reboot their devices in safe mode, and uninstall the malicious app from there if they have already detected it, but this method may prove too difficult for most users.
http://www.tomshardware.com/news/tre...oid,29871.html
-
20-08-15, 10:37 #63Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Galaxy S4, Nexus 7, and HTC One M8 Receive Stagefright Lollipop Update
Considered as one of the high-risk security vulnerabilities discovered in Android operating system, carriers have started rolling out updates to fix the exploit. We shared with you yesterday a complete guide to manually flash Android 5.1.1 on Samsung Galaxy S5 fixing the Stagefright vulnerability.

Stagefright fix arrives for more devices today:
Google and carriers are working to roll out this critically important security update as soon as possible. Stagefright bug allows attackers to take control of your data and steal data from the devices. In the latest run, Nexus 7, Samsung Galaxy S4 and the HTC One M8 have received the Stagefright exploit fix. These three updates have come from Verizon and Sprint. Here are the details about which devices are getting what update:
- Samsung Galaxy S4 has received the LRX22C.I545VRUGOF1 Android 5.0.1 from Verizon to patch the bug; update also brings stability tweaks.
- Android 5.1.1 incremental update from Verizon for Nexus 7 bringing all the Material Design goodies.
- And, Sprint has rolled out Android 5.0 Lollipop update for HTC One M8 to patch the exploit with no other changes.
Regardless of the serious risk that Stagefright poses Android users to, all these three (and other similar future updates for different devices) will be rolled out in multiple phases in different regions. Let us know if you have received the notification already on your devices. If you think you might have missed the notification, you can go to Settings > About Device > Software Updates > Check Now to confirm if you have got the update notification from your carrier. If you have indeed received the firmware update notification, click to download it. Once done, move forward with the installation. Make sure you charge your devices to at least 60% before starting the installation process.
Don’t forget to share if you have received the update on your devices. Please share your region, carrier, and device names for our readers to get a clue on when to expect this patch from their carrier.
-
22-08-15, 13:23 #64Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Update Galaxy S3 to PACMAN Android 5.1.1 Lollipop – How to
PACMAN custom firmware based on Android 5.1.1 Lollipop is now available for AT&T Samsung Galaxy S3 I747. While there is no hope of Lollipop coming to Galaxy S3, you can taste all the features and much more with this beautiful and stable custom ROM. Here are all the PACMAN Android 5.1.1 features for Samsung Galaxy S3 I747 followed by a complete guide to help you flash the custom ROM on your own smartphone.

Prerequisites to flash Android 5.1.1 on Galaxy S3 I747:- Backup any important data from your Samsung Galaxy S3 SGH-I747 as a complete wipe will be required during the flashing process.
- Enable USB debugging option on your device: Settings > Development Options > USB debugging.
- Samsung Galaxy S3 must be rooted, unlocked and installed with a recovery tool like TWRP or CWM.
- Your device must be charged to at least 60% of power.
Note: this tutorial is focused on AT&T Samsung Galaxy S3 SGH-I747; kindly do not try this guide on other Android & Samsung devices.

How to update Galaxy S3 I747 to Android 5.1.1 PACMAN:
Required files: download the PACMAN Android 5.1.1 Lollipop custom firmware for Galaxy S3 I747. and save it on your computer. Also download GApps package. Do not extract the contents.
- Connect Galaxy S3 to your computer using a USB cable and copy the zip file to your phone’s SD card.
- Disconnect the USB cord and power off your Galaxy S3.
- Boot it into recovery mode by pressing and holding Volume Up + Home + Power buttons together.
- Perform a Nandroid backup of your current OS: Backup > backup and restore on ClockworkMod recovery.
- Wipe data task: from CWM recovery menu, select wipe data / factory reset and confirm the process. Then go on to wipe cache partition and wipe dalvik cache.
- From recovery menu, select install zip from sdcard followed by choose zip from sdcard. Locate the PACMAN Android 5.1.1 Lollipop custom firmware and confirm the flashing process.
- Return back to main recovery menu and reboot your AT&T Samsung Galaxy S3 into the new custom ROM. First boot takes a good 5 minutes so please be patient.
How to restore: If you want to return to previous OS on your SGS3, boot into recovery, select backup and restore then restore your previous ROM by selecting it from the list.
-
27-08-15, 08:15 #65Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Cortana speaks fluent Android
Noticia:
Hands on: We just tried it
Microsoft promised Cortana was coming to Android, and this is now happening, at least for users in the USA.
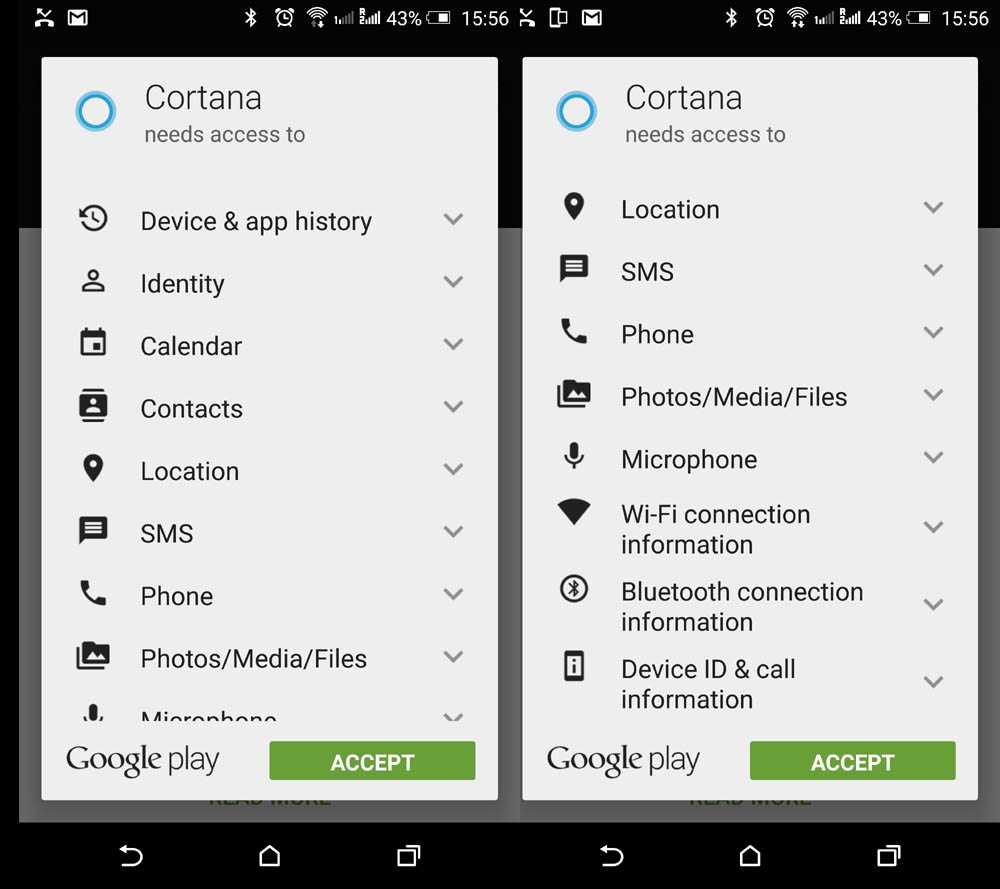
Fudzilla was among the first thousand Android users to install and try this new piece of software. It is a 20MB download that installs rather quickly.
We were not surprised that Microsoft wants just about every possible detail you can imagine from your location, phone call list, SMS, photos, microphone to the Wifi and Bluetooth. They want to know everything probably to sell you better adds in addition to providing the smart assistant service.
Once you install the Cortana android application you will be asked to enter your Microsoft user name and password. After that you are good to go. We asked Cortana how long was the Golden Gate bridge and it knew the answer – 8980 feet or 2737 meters.
First time Cortana thought we asked it how long is to Golden Gate Bridge and we got a funny answer that it didn't think we can get there by car which was sort of true. We were 5979.1 miles away when we asked the question.
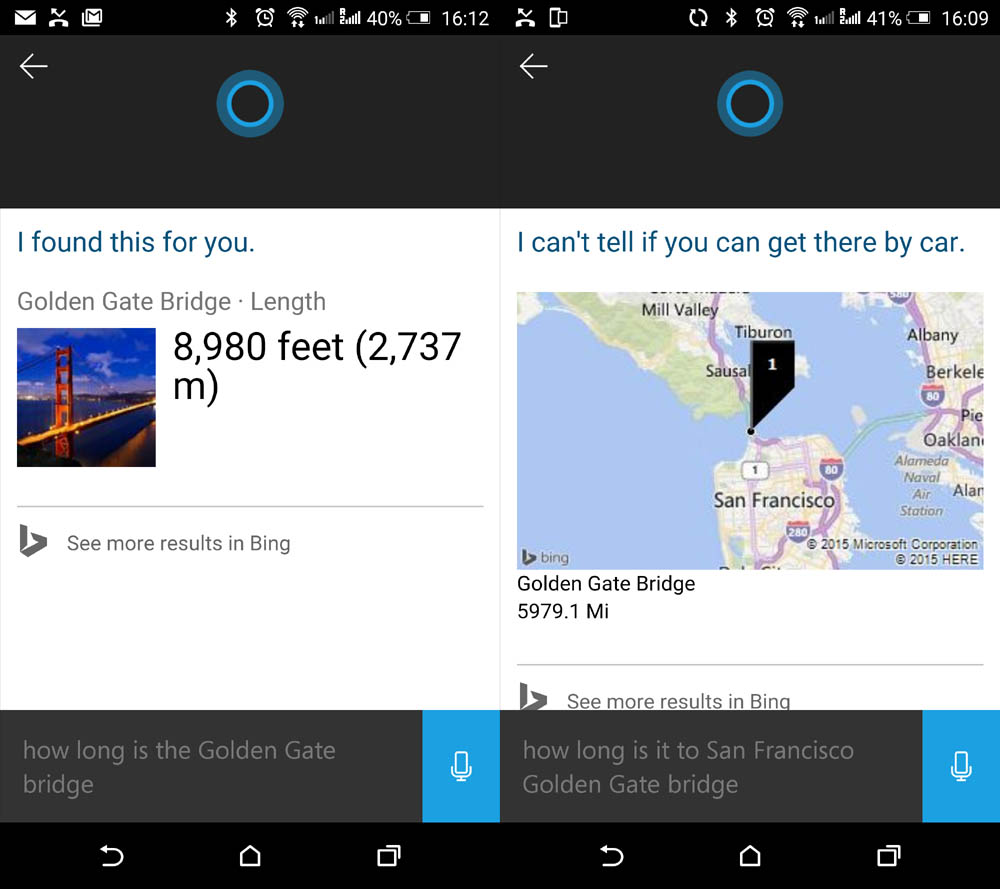
Cortana also knows that Angela Merkel is in Vienna today, we guess she asked the NSA as they tend to keep tabs on her. There were a few other things it knew. It gave us an answer about Microsoft stock that got up 1.9 percent to $41.27 while we wrote the story – clearly someone in Wall Street was betting on a positive review.
Swiping up the home button will ofer you a choice between Google Now and Cortana, until you set one of them as default application. We used both after each other and got similar results for the basic questions.
Cortana can tell you the ages of all the women from the Friends telly show and all the other important questions.
You can use Cortana to change your 3 PM appointment to 4PM. The only way we got it stumped was when we asked Cortana to tell us a joke.
http://www.fudzilla.com/news/mobile/...ks-android-now
-
27-08-15, 08:37 #66Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
AMIDuOS Turns Two: Lollipop Support And A Price Change
Noticia:AMI announced version 2.0 of its AMIDuOS software, bringing feature compatibility with the latest Android OS. AMIDuOS is software that runs Android in a virtual machine that can be used by consumers to run Android programs on a PC, or by programmers to develop and test apps.
AMI also shifted its pricing of these products in order to accommodate offering the older AMIDuOS V1.x software alongside the V2.0 software.
The primary features that version 2.0 offers are expanded support for Android 5.0.1 and 64-bit programs. Although the beta version released last month first demonstrated these functions, v2.0 can be seen as a more stable solution. It is also more feature complete, moving to Lollipop 5.0.1, rather than the Lollipop 5.0 version used in the beta.
The latest version is also compatible with the Android ART runtime environment and hosts new APIs for Bluetooth LE, multi-networking, NFC and other standards. These improvements, in addition to AMIDuOS's typical A/V sync improvements, graphics improvements and audio improvements, makes it an even better tool for testing and developing Android applications.
Realizing that devices utilizing the 32-bit Android 4.x are still widely used, AMI opted to continue to sell V1.x of AMIDuOS alongside the version 2.0 release. This gives users a greater range of options when it comes time to test their applications. If required, both versions of AMIDuOS can be installed on the system side-by-side without any conflicts.
For users who have been using AMIDuOS for a long time and now want to try version 2.0, there's no need to break out your wallet. AMI opted to give anyone who purchased AMIDuOS v1.x prior to August 7, 2015 a free copy of version 2.0. This offer is available indefinitely, and users who download the latest AMIDuOS can continue using their older version, as well.
If you purchased AMIDuOS between August 7 and today, however, then you will not be eligible for a free copy of AMIDuOS v2.0. In order to continue to offer both products, AMI will continue to sell V1.x for $10 as it always has, and offer V2.x for $15.
The latest AMIDuOS is available now.

http://www.tomshardware.com/news/ami...n-2,29929.html
-
09-09-15, 08:02 #67Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Flash CM 12.1 Stable Android 5.1.1 on HTC One M7 – How to
The CM team started releasing stable builds of CyanogenMod 12.1 for various popular flagship devices last week. We already shared with you the links to flash CM 12.1 Nightlies on your smartphone, here is how you can now experience more stable performance with one of the most popular custom firmware for Android devices. Follow this guide to flash CM 12.1 Stable ROM on your HTC One M7.

Prerequisites to update HTC One M7 to CM 12.1 Stable Android 5.1.1 ROM:- Backup any important data from your HTC One M7 as a complete wipe will be required during the flashing process.
- Make sure ADB and Fastboot is configured on your PC.
- Your device must be rooted with unlocked bootloader and installed with a recovery tool.
- Your device must be charged to at least 60% of power.
How to update HTC One to CM 12.1 Stable Android 5.1.1:
Required files: download CM 12.1 Stable Snapshot file for HTC One M7 and save it on your computer. Also download Google Apps Package.
1- Connect your HTC One M7 to your computer using a USB cable and copy the zip file and GApps to your phone memory’s root folder.
2- Switch off your HTC One M7 and enter into Recovery mode: press and hold the Volume Down and Power buttons.
3- Select Backup and Restore to perform Nandroid Backup and then go back to main menu. Next, you must wipe data by selecting wipe data/factory reset.
4- Now, select Install zip from sdcard > choose zip from sdcard from the main recovery menu. Locate the CM 12.1 Stable Android 5.1.1 custom ROM for HTC One M7. Select and confirm.
5- When the CM 12.1 custom ROM is flashed, use the same method to install GApps. After you are done, select reboot system now to perform a normal boot. It will take some time to load all files as the first boot takes more time.
-
09-09-15, 21:10 #68Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Lollipop Graces One Out Of Five Android Devices As Marshmallow Comes To Town
It's been just over 10 months since Android 5.0 Lollipop was first made available to the general public, and in that time, it's found its way onto one out of every five Android devices. If you'd prefer to take the glass half empty approach, you can point out that four out of five Android devices are still waiting for Lollipop, Marshmallow be damned.
According to the data by Android Developers, Android 5.0 is installed on 15.9 percent of Android devices, while Android 5.1 (also Lollipop) adds another 5.1 percent. That comes out to an even 21 percent.

The majority of Android devices these days are rocking Android 4.4, otherwise known as KitKat. It holds a 39.2 percent share of the Android device market, followed by versions 4.1.x through 4.3 (Jelly Bean) at 31.8 percent, 2.3.3 through 2.3.7 (Gingerbread) at 4.1 percent, 4.0.3 through 4.0.4 (Ice Cream Sandwich) at 3.7 percent, and version 2.2 (Froyo) at 0.2 percent.
We know, rattling off a bunch of numbers is about as interesting as listing to someone describe how drunk they got the night before at a frat party, or recount how they got screwed by the river in a Texas Hold 'Em tournament after going all-in. It's the story behind the numbers that matter, which in this case is that the most prevalent version of Android is soon to be two generations old.
The issue of fragmentation is one that Google has yet to solve, perhaps because Google doesn't view it as a problem. After all, if you want to always have the latest and greatest version of Android, you can purchase a Nexus device or get into the third-party ROM scene.

Those options are of little consolation to Android device owners waiting for their handset maker and wireless carrier to dole out an update to Lollilop, which will still put them a generation behind once Marshmallow rolls out.
Speaking of which, Marshmallow is expected to be available to the general public by the end of the month. Despite the jump to Android 6.0, it's more of an incremental upgrade with a focus on bug fixes and other backend improvements.
-
11-09-15, 10:09 #69Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Android Stagefright Exploit Released To The Public
Noticia: Zimperium, the security company that initially found the vulnerabilities in Android's Stagefright media library, promised on August 5 that it would release an open source exploit for testing purposes. The company has now released the exploit in the wild to get Android OEMs to hurry up and deliver the patches to their devices, but also to allow other security experts to test whether their devices are still vulnerable.
Zimperium, the security company that initially found the vulnerabilities in Android's Stagefright media library, promised on August 5 that it would release an open source exploit for testing purposes. The company has now released the exploit in the wild to get Android OEMs to hurry up and deliver the patches to their devices, but also to allow other security experts to test whether their devices are still vulnerable.
Exploit in the wild
The publicly released exploit is not a "generic exploit," the company said, because it has only tested it on an older Nexus running Android 4.0.4. The Stagefright vulnerability used for the exploit has been neutered by Android 5.0's use of the GCC 5.0 compiler, which comes with integer overflow mitigation.
Zimperium's release of the exploit doesn't necessarily make it that much easier for attackers to exploit Stagefright, as other exploits have already been created that can even bypass Android's address space layout randomization (ASLR) protection, and there are likely to be more out there that we don't know about.
Upgrades still in poor shape
So far only Google (Nexus devices), Samsung, and LG have promised monthly security updates after the Stagefright vulnerabilities were first made public. However, a few other companies such as Motorola, HTC, Sony and others also started sending Stagefright patches for some of their devices.
The main problem here is that none of these companies are going to patch most of the exploitable devices, which includes all Android 2.3 devices and beyond, covering over 900 million smartphones and tablets. At best, the majority of the OEMs will upgrade their most popular devices from the past two years, and that's about it.
Because Google is not responsible with the updates for the Android ecosystem, that pits Android OEMs in a price race to the bottom, where the costs of developing new updates for smartphones gets discounted as unimportant, compared to other priorities such as using a better camera, processor or screen, or simply having a lower price than the competition. This situation may never be fixed by itself until Google takes the whole responsibility upon itself (and the OEMs allow it to do that).
Initial quick-fixes not enough
The Stagefright vulnerabilities were indeed a wake-up call for Google as well as some manufacturers but were unlikely to be big enough to make them consider a significantly improved upgrade system. After all, only three companies promised monthly security updates, and even they didn't say for how long that will be in place for certain devices, or whether all devices will be under the new update program.
Some apps such as Hangouts and Messenger have also been updated by Google to resist Stagefright exploits, considering the easiest way to attack a user is through an MMS or other video file sent to SMS or other messaging apps that have auto-retrieval of video files enabled.
However, this isn't the only way users can be attacked. They can also receive video files through the browser when visiting a website. Typically, the user would have to accept such a file, though, so the risk there is minimized.
Checking for Stagefright vulnerabilities
To check whether you're still vulnerable, you can use Zimperium's Detector app. The app now also checks against the bugs in the Stagefright library, which were unveiled shortly after the first Stagefright announcement was made by Exodus Intelligence. Patches for these latest bugs haven't been distributed to many devices yet, though, as they are set to arrive in the next batch of official upgrades from Android OEMs (which could be a few weeks for Google, LG and Samsung, or a few months for others).
Zimperium has also collaborated with Google to include the Detector app's logic into the Android Compatibility Test Suite (CST) to ensure that all new smartphones will be protected against these vulnerabilities.
http://www.tomshardware.com/news/and...sed,30056.html
-
07-12-15, 17:59 #70Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Samsung Introduces Android 6.0 Security Feature in a Latest Lollipop Update
Google has been trying to push its partners to be more proactive in sending Android security updates to their consumers. Since the discovery of a major security threat, Stagefright which put over a billion of Android users at risk, there has been a lot of uproar from the users as well. As Apple leads the game when it comes to sending timely and consistent security updates and Microsoft, with its nascent Windows 10 Mobile, intends to take charge of OS updates, all the eyes are then pinned at Android and how it moves forward to offer more mobile security and privacy to the users.
– Recommended: Samsung redesigns TouchWiz before releasing Android 6.0 Marshmallow

Samsung offers Marshmallow feature in Lollipop to improve Android security:
Google’s OEM and carrier partners committed to send monthly security patches to their users, released by Google. Among these, Samsung also promised to keep its “high-end” devices up-to-date with security updates. However, it wasn’t until now that you could actually see Samsung being more proactive about it. After the Stagefright-episode, Google introduced a security feature in Android 6.0 Marshmallow that showed the date the device last received a security update, in order to put more pressure on its partners giving them public visibility. As reported,
This security update date would let the users know when their devices last received the security update, promised by many manufacturers. While it is not an aggressive measure from Google to push mandatory monthly updates, the tactic will help put some light on those who are lagging behind in sending out these updates.Latest Lollipop update rolled out to Samsung devices has now updated the About Phone section of the Settings menu which shows exactly the same Marshmallow feature – the date of last security patch delivered to a device. Folks at Android Central report that Samsung Galaxy S6 Edge+ builds (G928FXXS2AOK9) in Europe and Galaxy Note 5 (N920CXXU2AOK6) users in the Middle East have confirmed this new security addition.
Advertisements
Similar to Android 6.0 Marshmallow, the new Lollipop firmware on Samsung devices shows a field “Android security patch level,” showing a date when the phone last received a security update from Samsung. To confirm if you too have received this latest feature, go to Settings, and scroll down to About Phone. Don’t forget to let us know which Samsung device you own, if you too have received this update.
VIA
-
20-02-16, 16:18 #71Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Multiple Motorola Devices Will Not Be Upgraded to Lollipop
Noticia:
These days we are being told that we need to install or swap out software and hardware all the time to keep it up to date. With everything from Windows Updates recommending a whole new operating system to a “security update” locking up your iPhones. When I decided to try out Windows Mobile (when it was first released) I liked the OS, except that it didn’t support anything. To my surprise (or not as the case was) they decided that my handset would be one of the ones that wouldn’t get the Windows 8 Mobile upgrade, leaving my phone outdated and out supported. It would seem that Motorola made the same decision with the Droid Ultra, Maxx and Mini editions regarding the latest Lollipop update.
On their forums Motorola posted the following:
“We apologise that we will not be upgrading DROID Ultra/Mini/Maxx to Android Lollipop, as we had hoped. We know how important software upgrades are to our customers, and we’re very sorry that we are unable to provide the upgrade.”In an attempt to bring back any customers upset by this those with the Ultra/Mini or Maxx handsets can upgraded to the DROID Turbo 2 for $524 or the DROID Maxx 2 for $334.
The worst part about all of this is that the upgrade was promised and now instead of delivering on that promise they want you to pay for a new handset. No doubt this is going to upset anyone with one of the mentioned headsets, are you one of those people and if so how do you feel about this?
http://www.eteknix.com/multiple-moto...d-to-lollipop/
-
09-03-16, 20:39 #72Tech Ubër-Dominus


- Registo
- Nov 2013
- Local
- City 17
- Posts
- 30,121
- Likes (Dados)
- 0
- Likes (Recebidos)
- 2
- Avaliação
- 1 (100%)
- Mentioned
- 0 Post(s)
- Tagged
- 0 Thread(s)
Lollipop Now Most Popular Version Of Android, Fluffy Marshmallow At Just 2.3 Percent
Noticia:Comparatively speaking, there aren't a lot of Android devices in the wild running Android 6.0, otherwise known as Marshmallow. That's typically true of any snapshot of Androidthe latest and greatest version finds its way onto just a small number of handsets while versions a generation or two old rule the roost. As of right now, pole position belongs to Android 5.x Lollipop.
It took Lollipop more than a year16 months, to be exactto leapfrog Android 4.4 KitKat for the top spot. But there it now sits, at least if combining the number of devices running Android 5.0 (16.9 percent) and Android 5.1 (19.2 percent). If you add the two together, Lollilop's share of the Android market is 36.1 percent, versus 34.3 percent for KitKat.
One thing to note is that these aren't exact figures. Google tallies the number of Android devices running different versions of its mobile operating system by collecting data over a seven-day period gathered from its Google Play Store app. That means Google's data is a reflection of devices that have checked into Google's servers. It leaves out some rooted devices, Amazon Fire tablets, and so forth.
While it's not a perfect accounting method, it's the best that's currently available. And as always, what it shows is that hardware manufacturers and wireless carriers are slow to adopt the latest version of Android. Marshmallow was made available to the general public five months ago, yet it's tied with Android 4.0 Ice Cream Sandwich for fifth place behind Android 2.3 Gingerbread, which debuted over five years ago.
It's a familiar trend and one that isn't likely to change so long as control of distributing Android builds remains in the hands of third parties. This is especially true of older devicesmanufacturers don't have a lot of incentive to keep supporting dated phonesbut even some newer phones are slow to adopt updated Android builds.
Do you own and Android device? If so, which one and what version of Android are you running?
http://hothardware.com/news/lollipop...aAFV4jbA71b.99
Informação da Thread
Users Browsing this Thread
Estão neste momento 1 users a ver esta thread. (0 membros e 1 visitantes)







 Responder com Citação
Responder com Citação

Bookmarks